Database Performance Optimization Service
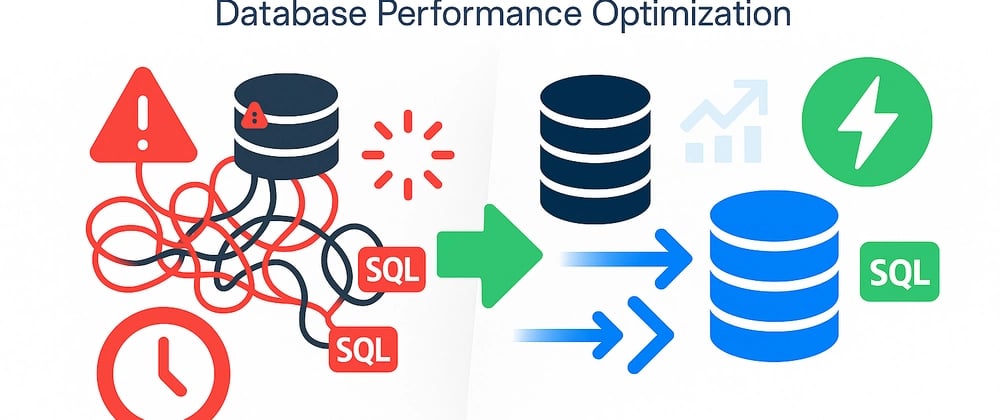
Our Database Performance Optimization Service is designed to maximize the speed, efficiency, and reliability of your database systems. Through detailed performance assessments, query tuning, indexing strategies, and configuration enhancements, we ensure your databases operate at peak performance—supporting faster transactions, improved scalability, and higher availability for business-critical operations.
Improve query response time and transaction speed.
Fine-tune CPU, memory, and storage performance.
Identify and resolve slow-running processes.
Ensure databases perform optimally under heavy loads.
Maintain consistent and reliable database operations.
